Security Automation
Security Automation for Pipelines
Embed SBOM generation, secret scanning, and policy gates without turning every build into a noisy gatekeeper.
- Duration
- 5 weeks
- Format
- Cohort
- Skill level
- Advanced
- Certification track
- Security automation path
₩780,000
Tuition is informational on this static site—no checkout or payment capture here.

You wire pragmatic controls into CI, tune severity thresholds, and design exception workflows auditors can follow. The tone stays engineering-first: fewer slides, more diffs.
What is included
- SBOM generation with storage and retention policy
- Secret scanning tuned for monorepos
- Container image signing walkthrough
- Policy-as-code snippets for Kubernetes and CI
- Vulnerability triage rubric for developers
- Evidence pack layout for security reviews
- Tabletop for a poisoned dependency scenario
Outcomes
- Attach an SBOM artifact to every mainline build
- Land one policy gate with documented override path
- Produce a triage note developers considered fair, not adversarial
Lead instructor
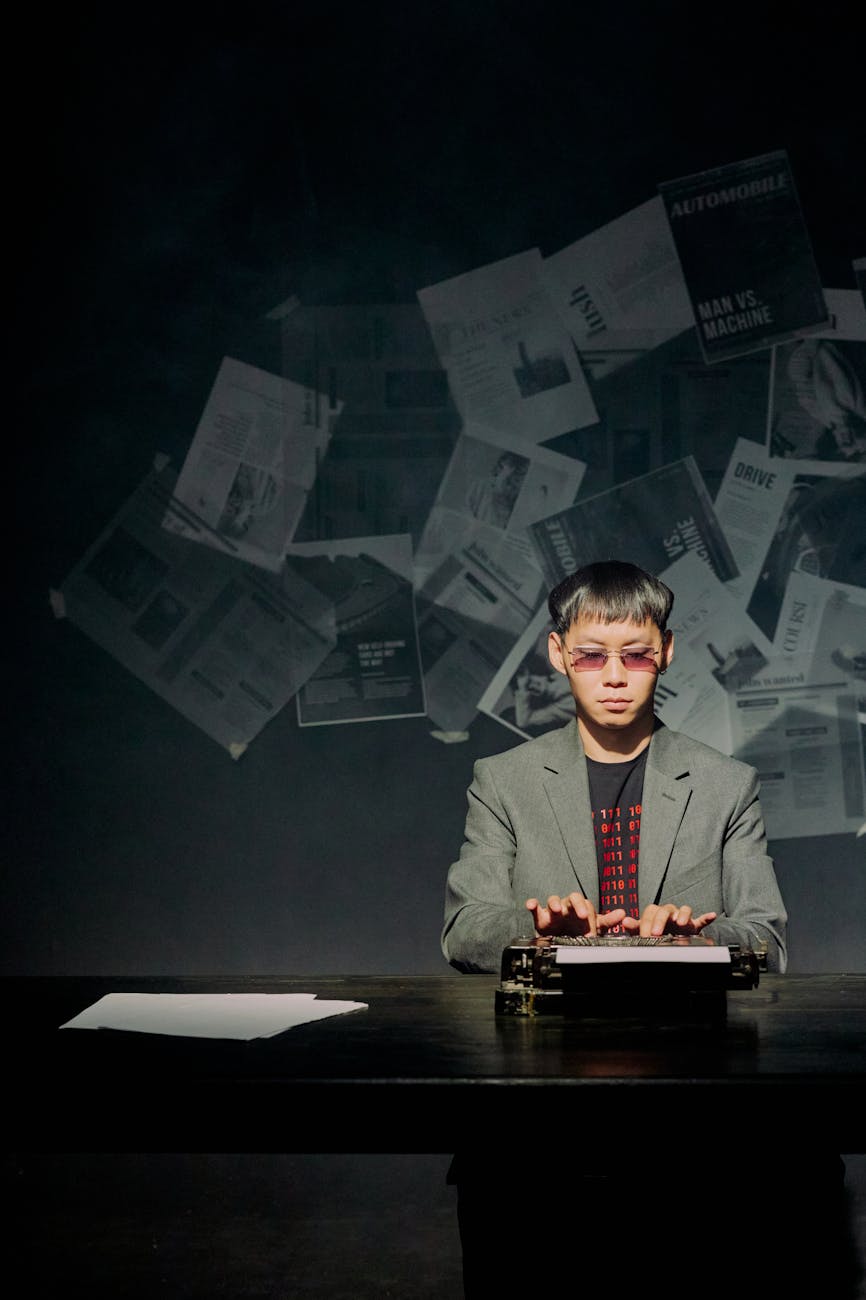
Theo Rhee
Enterprise account manager bridging security asks with delivery reality.
FAQ
Recent participant notes
SBOM lab mirrored our Artifactory layout. Policy gate noise dropped after we applied their severity matrix.